
OT penetration test
Identify weak points, initiate measures
OT penetration test
Identify weak points, initiate measures
OT is mostly found in critical infrastructures such as energy generation plants or highly complex industrial production lines. But cyber attacks can also lead to outages, business losses or image damage in conventional OT facilities. Do you know your attack surface? Do your control mechanisms work? An OT penetration test provides clarity.
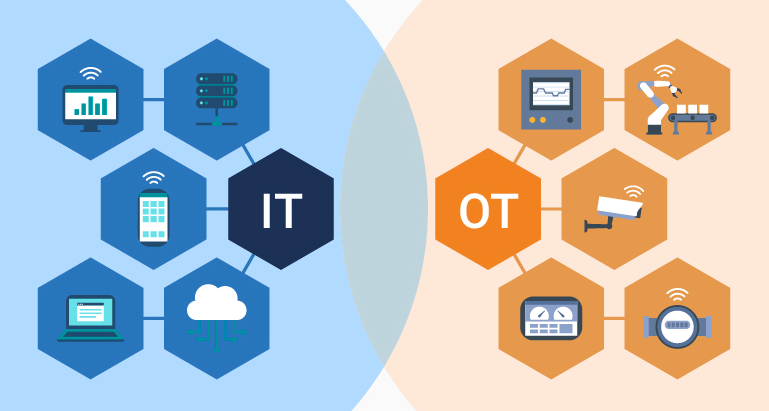
What is OT?
Operational technologies (OT) are generally defined as «hardware and software that control and monitor industrial equipment». The term has become established to highlight the technological and functional differences between traditional IT and industrial control systems (ICS), which are more mechanical and physical in nature.
Note the difference between IT and OT penetration testing
OT environments are traditionally operated differently from traditional IT environments and, for this reason, face different security challenges. They are often older and more prone to failure, which is important for the technical auditor to consider and which has a strong influence on the way the test is planned.
Based on this knowledge, terreActive has developed a penetration test specifically designed for OT environments. When conducting it, we pay special attention to live systems, using a fully manual testing methodology. Incidents from Europe show that operations commonly performed in classical tests, such as a vulnerability scan, can cause the target system to malfunction. In the case of an industrial plant, this can lead to a slowdown or even a standstill of the production process, which in turn results in loss of business.
Our experience
terreActive carries out around 30 OT penetration tests per year and has in-depth knowledge in this area.
We point out the above-mentioned challenges to our customers in advance and pay great attention to serious planning.
Scope of OT penetration test
- Purely technical testing of the areas defined in advance
- Different perspectives to choose from, e.g. hacker or compliance view, internal or external
- Different systems can be tested, e.g. selection based on IP ranges
Benefit OT pentest: What is examined?
- Do we find vulnerabilities that could lead to an attacker or malware penetrating the company's network?
- Are there any unusual services? Are services co-located on a server for which separate hosting is recommended?
- Are OT management interfaces properly protected? Is access to the system granted only to those who need it?
- Is TLS present on all services? Are exceptions acceptable and does the TLS configuration follow current recommendations?
- Is there a separation between IT and OT environments?
- Is there evidence of outdated operating systems or software components with vulnerabilities?
Result (Output)
- Report with Executive Summary
- The report contains results and analyses, evidence and recommendations for action.
- The presentation and discussion of the report takes place online or on site
Selectable options
- External information gathering and OSINT (Open Source Intelligence = information from freely available sources)
terreActive checks the exposure of your OT systems to the Internet
You can find out more about terreActives consulting services on our audit page.
